Network Policy Capabilities
To effectively manage a modern network, visibility into applications, protocols, and cybersecurity must be translated into concrete, enforceable network behavior. Netify Flow Actions bridges this gap by turning high-level intelligence into precise policy control:
- Firewalling: Dynamically restricting or allowing access based on high-level network attributes rather than just IPs.
- Quality of Service (QoS): Prioritizing latency-sensitive traffic (like VoIP) or throttling bandwidth-heavy services (like file sharing) to ensure a high Quality of Experience (QoE).
- Routing: Directing specific applications or protocols over preferred paths.
Netify Flow Actions
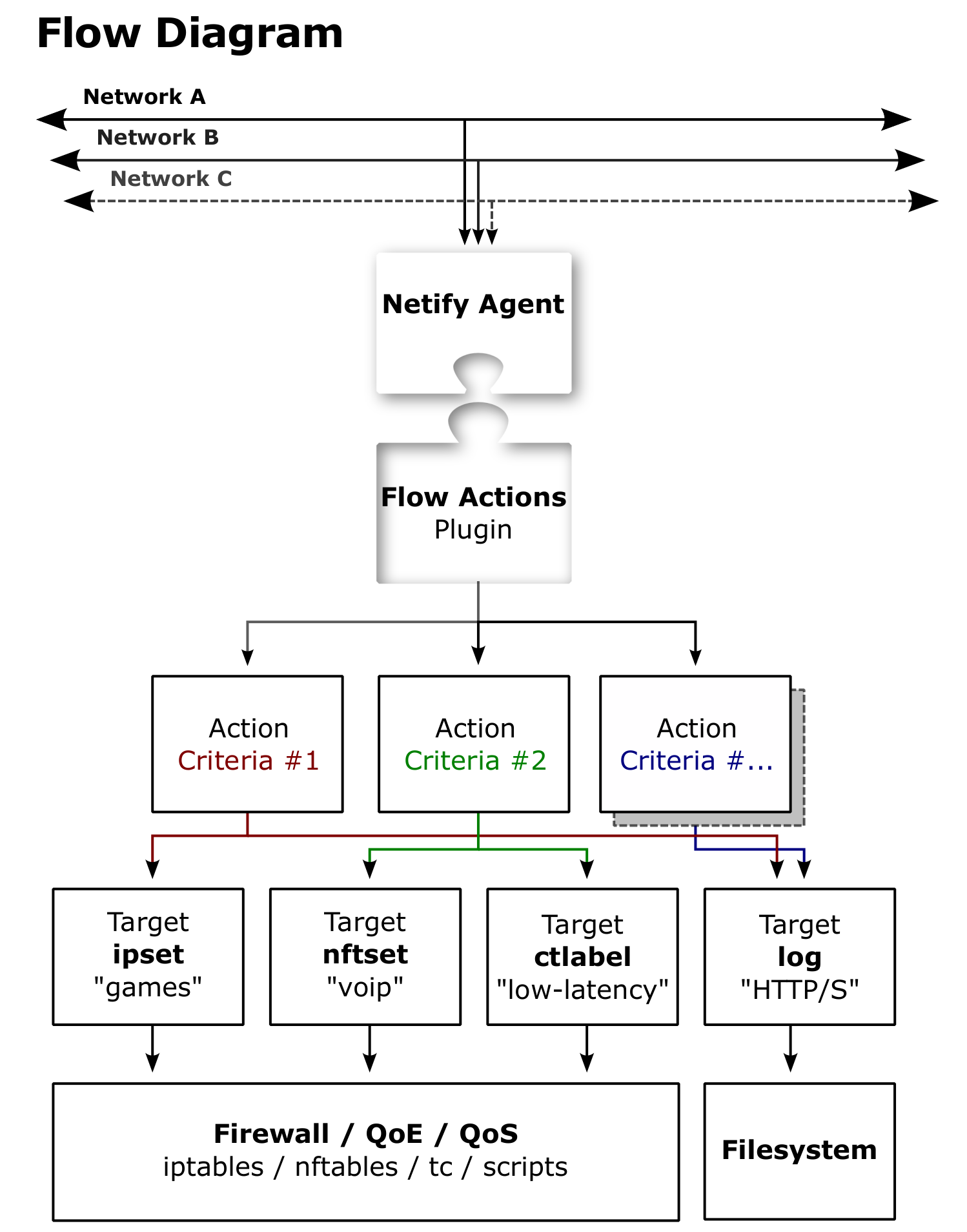
Netify Flow Actions bridge deep packet inspection (DPI) intelligence with real-world network enforcement. As the Netify DPI Agent identifies applications, protocols, and categories in live traffic, the Flow Actions plugin evaluates each new flow in near real time against user-defined criteria. When a match occurs, the flow is immediately acted upon, turning visibility into precise control over network behavior.
At its core, the plugin serves as a high-performance interface between application-layer awareness and operating system-level mechanisms. It connects DPI-derived metadata to native OS components responsible for firewalling, traffic shaping, routing, and logging. This allows network operators to implement advanced policies using existing system capabilities on platforms like Linux and FreeBSD.
Flexibility is central to the design. Flow Actions supports both simple and advanced policy definitions, enabling traffic matching based on basic attributes like application or protocol, or more detailed expressions using full flow metadata. With a lightweight, reloadable JSON configuration and modular design, it can be adapted to environments ranging from embedded systems to high-throughput appliances — without code changes.
By mapping high-level network intelligence to actionable system controls, Flow Actions transforms DPI from passive observation into active enforcement. The following sections explore the supported mechanisms that make this integration both powerful and practical.
Supported Integrations
IP Sets
The IP sets integration leverages the Linux kernel's high-performance IP Sets framework to manage large collections of IP addresses, ports, or MAC addresses with minimal lookup latency.
Key Advantage
In addition to simple matching, it supports socket buffer (skb) attributes - allowing marks, masks, and traffic priorities to be applied directly to packets in-flight.
nftables Sets
The nftables set integration works with the modern nftables framework, enabling highly flexible and expressive rule construction.
Key Advantage
Supports multi-dimensional matching, combining attributes like IP address, port, and interface into a single rule for precise, context-aware enforcement.
Connection Tracking Labels
Connection tracking labels apply tags to connections within the kernel's state table, effectively tracking flows for their entire lifetime.
Key Advantage
Enables efficient reuse of classification results—once labeled, packets don't need to be re-evaluated by DPI or firewall rules.
Connection Tracking Marks
Connection tracking marks assign a 32-bit value to each connection, acting as a standard signaling mechanism between the network stack and external subsystems.
Key Advantage
Universally supported by Linux networking tools, making it the most effective way to hand off decisions to downstream systems like traffic shaping or routing engines.
pftable (FreeBSD)
The pftable integration operates directly with the pf subsystem used in FreeBSD-based systems such as pfSense and OPNsense.
Key Advantage
Native, high-efficiency enforcement within pf tables, delivering near-zero overhead for dynamic rule updates.