Audit and Forensics
Netify Informatics - Audit and Forensics
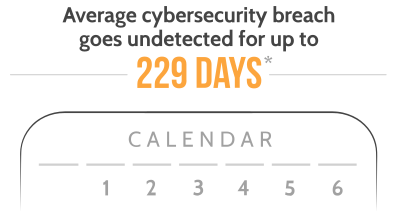
It only takes one data breach, or cybersecurity event to put a serious dent in a company's reputation and bottom line. Keeping detailed records of who or what is operating on the network helps detect and manage risks.
Netify Informatics network monitoring APIs can be used like an audit trail for the network in the same way a system audit tracks all user and system activities. Informatics keeps a history of traffic flows on the network and can help identify points in the past where there was suspicious activity - like connections to known phishing websites.
Historical Network Intelligence - Log Network Traffic
Historical connection tracking data can be hugely valuable to organizations in several scenarios. For example:
- Analyzing network performance issues
- Investigating a security breach or malware infection
- Demonstrating compliance for regulatory agencies
Netify Informatics flow activity history is a valuable piece of Network Intelligence that can be key in determining where a security breach took place, how it happened, and where the main vulnerabilities might be.
Also, when consulting with a cybersecurity forensics team, the Informatics' historical DPI flow metadata saves time and resources by providing the kind of accurate, detailed information needed to properly assess the network's cybersecurity risk, and prevent future breaches.
Integration and Custom Solutions
Do you have any questions about integration, APIs or custom development?
Contact Us